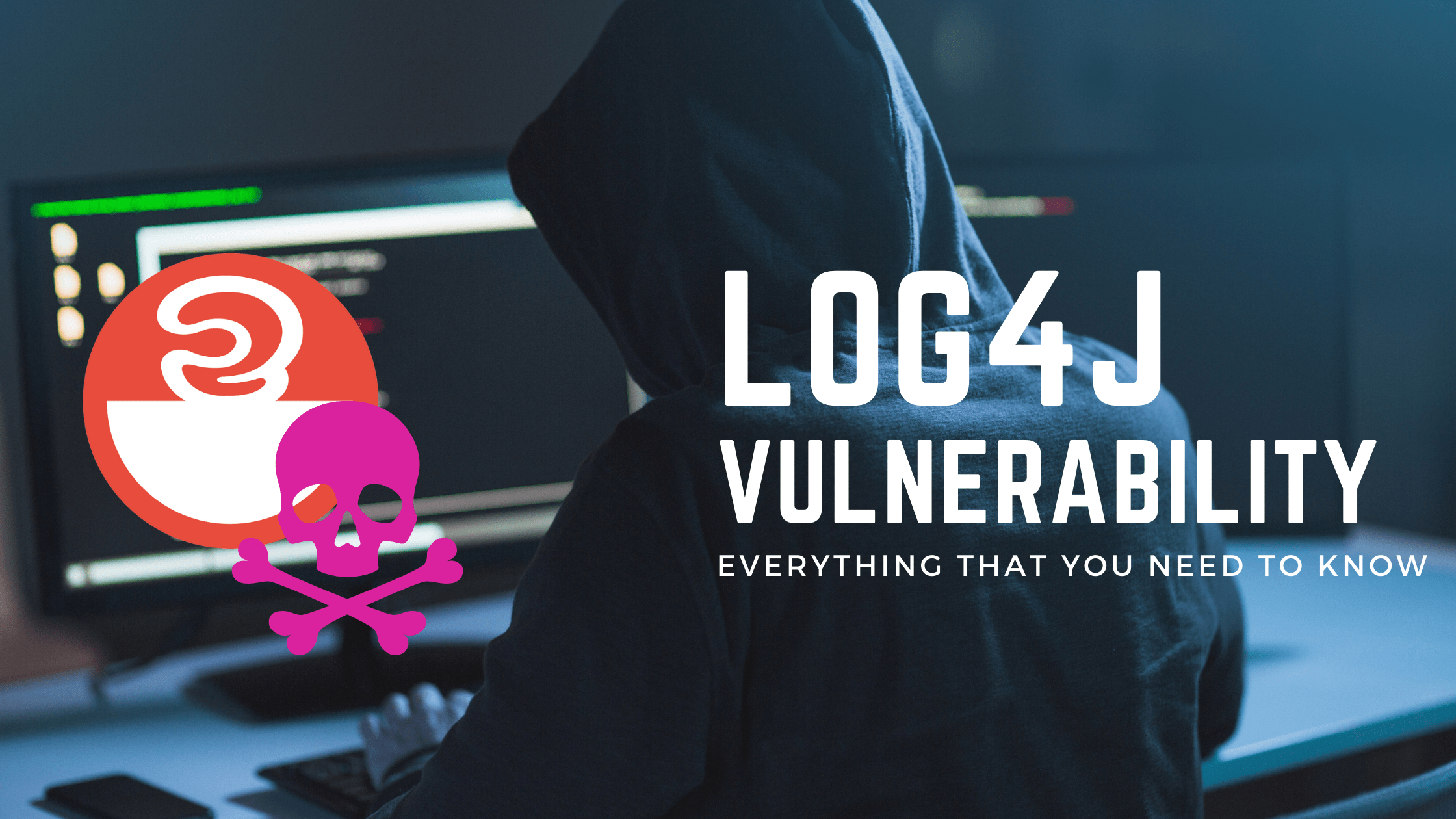
Everything You Need to Know about the Log4j Vulnerability
Apache Log4j is a logging tool written in Java. It’s part of the Apache Software Foundation’s Apache Logging Services project. One of the numerous Java logging frameworks is Log4j.
The Apache Log4j team created Log4j 2 in response to concerns with Log4j 1.2, 1.3, java.util.logging, and Logback, and to address issues with those frameworks. Furthermore, Log4j 2 had a plugin architecture, making it more extensible than its predecessor. Although an adapter is available, Log4j 2 is not backwards compatible with 1.x versions.
The Alibaba Cloud Security Team revealed a zero-day vulnerability involving arbitrary code execution in Log4j 2 on December 9, 2021, with the descriptor “Log4Shell.” Tenable describes it as the single most significant and important vulnerability of the previous decade. December 9th is now known as the day when the internet was set on fire.
Log4shell is a major flaw in the widely used logging programme Log4j, which is used by millions of machines running internet services across the world. It is expected to influence a wide spectrum of people, including organisations, governments, and individuals. Despite the fact that patches have been published, they must still be installed.
What’s the problem with Log4j?
Attackers can break into systems, steal passwords and logins, extract data, and infect networks with malicious software if the problem is not fixed.
Log4j is widely used in software and online services around the world, and exploiting the vulnerability needs very little technical knowledge. As a result, Log4shell could be the most serious computer vulnerability in years.
The latest number suggest that over 1.2 Million attacks were launched so far and if as of today, there’s no end in sight. The first patch proved ineffective for some versions and applications, which lead to a second patch release.
Who is this affecting?
Almost any programme will have the ability to log in some way (for development, operations, and security), and Log4j is a popular component for this.
Log4j is almost definitely a part of the devices and services you use on a daily basis if you’re an individual. The best thing you can do to protect yourself is to keep your gadgets and programmes as current as possible and to update them on a frequent basis, especially in the coming weeks.
For businesses, it’s not always obvious that Log4j is used by web servers, online applications, network devices, and other software and hardware. This makes it the more important for every company to listen to our counsel and that of their software vendors, and to take the appropriate precautions.
Check the full list of affected software on GitHub.
What do you need to do now?
Patch, patch, patch. First and foremost, we strongly advise all businesses to upgrade any instances of Log4j to version 2.16.0 as soon as possible. On December 14, Apache released Log4j version 2.16.0 as part of a security update. Reviewing Apache’s notes on this page may be beneficial.
If you are unable to fully update Log4j-based products because they are maintained by a third party, contact your third-party contacts as soon as possible for new information. It’s possible that they released updates without informing you.
If you or any third-party suppliers are unable to keep up with software upgrades, we advise uninstalling or disabling Log4j until updates are available. This is especially important for any Log4j-based Internet-facing applications.
Neutralise Threats for Peace of Mind
Your IT Service Provider should be all over this vulnerability the same way we are patching the systems we are managing for our clients and talking to their vendors.
If you feel that your current provider isn’t delivering the necessary results, give us a call or book a 15-minute video call at a time that suits you. There’s no obligation to buy anything, ever. During this quick chat, however, we can discuss what a true technology success partnership looks like. Here’s our live calendar:
Here's our live calendar!
Questions: [email protected]
Sources:
What the Log4j vulnerability is, who is affected
Log4j – Apache Log4j Security Vulnerabilities
Continue reading:












Recent Comments