Microsoft 365 Business Standard vs Business Premium
Everything you need to know about Microsoft Business Premium and how it compares to Business Standard.
Microsoft has many different packages (E1, F3, 365 Business, Enterprise and so on) and they keep changing their names. It’s not unusual that you might lose track of how they go to market. We wrote this article to compare the two most common packages used by businesses in London, Surrey and the UK – Microsoft 365 Business Standard and Business Premium.
They sound similar and in terms of user experience, they do pretty much the same – you get the beloved Office applications, a whole lot of communication gimmicks and everything is cloud-based.
However, when we look into administration and cybersecurity, we can see massive differences that would justify the additional £5.70 per user and per month.
What is Microsoft 365 Business
Microsoft 365 is a cloud-based productivity suite that allows you to pursue your passion while running your business smoothly without worrying about your software toolset.
It is more than just Word, Excel, or PowerPoint as it combines best-in-class productivity tools with powerful cloud services, device management, and sophisticated security in a single, connected experience.
Wherever your work takes you, use professional email and calendaring to stay in touch with customers and coworkers.
With 1 TB of online storage per user, you can store, access, and share files from anywhere.
Microsoft Teams has group chat, online meetings, and calling to keep your teams on the same page.
System Requirements
According to Microsoft.
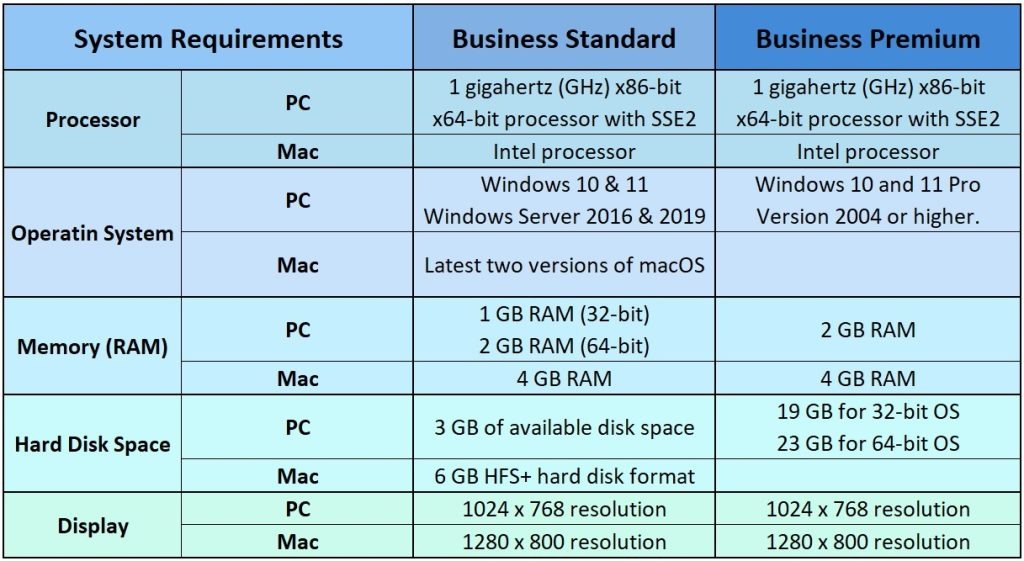
Internet functionality requires an internet connection and a Microsoft account is required.
Enterprise Mobility and Security Comparison
In this section, we are taking a good look at all the Enterprise Mobility and Security features that are available in Microsoft 365 Business Premium but NOT in Standard.
Azure Active Directory Premium
Microsoft Azure Active Directory is a comprehensive identity and access management cloud solution that combines core directory services, application access management, and advanced identity protection.
It includes:
✅ Cloud authentication (Pass-through authentication, password hash synchronisation)
✅ Federated authentication (Active Directory Federation Services or federation with other identity providers)
✅ Single sign-on (SSO) unlimited
✅ Multifactor authentication (MFA)
✅ Passwordless (Windows Hello for Business, Microsoft Authenticator, FIDO2 security key integrations)
Conditional Access
The current security perimeter now includes user and device identities in addition to an organisation’s network. Identity-driven signals can be used by organisations to make access control choices.
Conditional Access combines signals to enable decision-making and the enforcement of organisational policies. The new identity-driven control plane relies on Azure AD Conditional Access.
At their most basic level, Conditional Access policies are if-then statements: if a user wants to access a resource, they must first perform an action. For example, if a payroll manager wants to access the payroll programme, he or she must use multi-factor authentication.
Administrators are faced with two primary goals:
✅ Empower users to be productive wherever and whenever
✅ Protect the organisation’s assets
To keep your organisation secure, use Conditional Access policies to implement the appropriate access constraints as needed.
Self Service Password Reset for AD
Self-service password reset (SSPR) in Azure Active Directory (Azure AD) allows users to modify or reset their passwords without the need for an administrator or help desk.
If a user’s account is locked by Azure AD or they forget their password, they can unlock themselves and go back to work by following the steps. When a user can’t sign in to their device or an application, this capability reduces help desk calls and productivity loss.
Azure Information Protection
Azure Information Protection (AIP) is a cloud-based service that enables enterprises to identify, classify, and safeguard documents and emails by applying labels to content.
AIP is a component of Microsoft’s Information Protection (MIP) service, and it expands Microsoft 365’s labelling and classification capabilities.
The Azure Information Protection upgrades to MIP, including the unified labelling client, scanner, and SDK, are shown in the graphic below.
The common information protection stack used by AIP’s universal labelling client is Microsoft Information Protection.
Azure Rights Management
Azure Information Protection uses Azure Rights Management (Azure RMS), a cloud-based protection technology.
Azure RMS uses encryption, identity, and permission controls to safeguard files and emails across numerous devices, including phones, tablets, and PCs.
When employees email a document to a partner organisation or save a document to their cloud drive, for example, Azure RMS’ persistent protection helps secure the information.
✅ Protection settings remain with your data, even when it leaves your organisation’s boundaries, keeping your content protected both within and outside your organisation.
✅ Azure RMS may be legally required for compliance, legal discovery requirements, or best practices for information management.
✅ Use Azure RMS with Microsoft 365 subscriptions or subscriptions for Azure Information Protection. For more information, see the Microsoft 365 licensing guidance for security & compliance page.
Azure RMS ensures that authorised people and services, such as search and indexing, can continue to read and inspect the protected data.
Maintaining control of your organisation’s data requires ensuring continuing access for authorised people and services, often known as “reasoning over data.” Other information security solutions that use peer-to-peer encryption may not be able to achieve this feature as readily.
Microsoft Intune
Microsoft Intune is a cloud-based mobile device management (MDM) and mobile application management service (MAM). You have complete control over how your company’s devices, such as mobile phones, tablets, and laptops, are used.
To control applications, you can also set up custom policies. You can, for example, block emails from being sent to persons outside your company. People in your business can also use their personal devices for education or work using Intune. Intune helps ensure that your organisation’s data is protected on personal devices by isolating organisation data from personal data.
To regulate who has access and what they may access, Intune interfaces with Azure Active Directory (Azure AD). It also has a data protection integration with Azure Information Protection. It’s compatible with Microsoft’s 365 suite of products.
Microsoft Teams, OneNote, and other Microsoft 365 apps, for example, can be installed on smartphones. This feature allows your employees to be productive on all of their devices while keeping your company’s data safe thanks to the policies you set up.
You can do the following with Intune:
✅ Choose between being completely cloud-based with Intune or being managed jointly by Configuration Manager and Intune.
✅ Gain access to data and networks, create rules and modify settings on personal and corporate devices.
✅ Deploy and authenticate apps both on-premises and mobile devices.
✅ Control how people access and share information to protect your company’s data.
✅ Make sure your devices and apps meet your security needs.
Microsoft Defender for Office Comparison
Microsoft Defender for Office 365 protects your company from harmful threats such as email messages, URLs, and collaborative tools. The following list highlights only features that are NOT included in Microsoft 365 Business Standard but only in Business Premium.
Anti-Phishing
Phishing is an email assault that aims to obtain critical information via messages that appear to be from trusted or legitimate senders. Phishing can be classified into several categories. Consider the following scenarios:
✅ Spear phishing employs targeted, customised content that is tailored to the intended users (typically, after reconnaissance on the recipients by the attacker).
✅ For maximum effect, whaling is directed at executives or other high-value targets within an organisation.
✅ BEC uses falsified trusted senders (bank officers, consumers, trusted partners, and so on) to deceive receivers into approving payments, transferring funds, or divulging customer information.
✅ Ransomware, which encrypts your data and demands payment to unlock it, nearly always begins with phishing emails. Anti-phishing security won’t help you restore encrypted files, but it will help you notice the ransomware campaign’s initial phishing emails.
Anti-Phishing in Microsoft Defender for Office comes with impersonation security settings, mailbox intelligence settings, and customisable advanced phishing thresholds that can all be customised for specific message senders and sender domains.
Anti-Spoofing
Microsoft takes the problem of phishing very seriously when it comes to protecting its users. Attackers frequently use the method of spoofing. Messages that are spoofed look like they come from someone or somewhere other than the original sender.
This method is frequently employed in phishing efforts aimed at obtaining user credentials.
The anti-spoofing technology looks for forgeries of the “From header” in the message body (used to display the message sender in email clients).
Safe Attachments
Safe Attachments in Microsoft Defender for Office 365 adds an extra layer of security to email attachments that have already been checked by Exchange Online Protection’s anti-malware protection (EOP). Safe Attachments, in particular, employs a virtual environment to inspect attachments in email messages before they are sent to recipients (a process known as detonation).
Safe Attachments policies dictate how email communications are protected with Safe Attachments. Despite the fact that there is no default Safe Attachments policy, the built-in protection preset security policy offers Safe Attachments protection to all receivers (including those who aren’t defined in custom Safe Attachments policies). Safe Attachments policies can also be created for individual users, groups, or domains.
Safe Links
Safe Links is a feature in Defender for Office 365 that allows for URL scanning and rewriting of inbound email messages in mail flow, as well as time-of-click verification of URLs and links in emails and other places.
Inbound email messages are scanned by Safe Links in addition to the standard anti-spam and anti-malware security. Safe Links screening helps safeguard your company from harmful links used in phishing and other types of attacks.
Safe Links protection can be found in the following places:
✅ Emails
✅ Microsoft Teams
✅ Office 365 Apps
Add-Ons Comparison
The last section focuses on add-ons that are available with Microsoft 365 Business Premium but NOT with Business Standard.
Azure App Proxy
Azure Active Directory’s Application Proxy provides secure remote access to on-premises web applications. After a single sign-on to Azure AD, users can access both cloud and on-premises applications through an external URL or an internal application portal.
The Azure Active Directory Application Proxy is:
✅ Easy to use. Users may log in to your on-premises applications in the same way they log in to Microsoft 365 and other Azure AD-integrated SaaS apps. To use Application Proxy, you don’t need to replace or update your applications.
✅ Secure. Azure’s permission controls and security analytics can be used by on-premises apps. Conditional Access and two-step verification, for example, can be used in on-premises applications. You don’t have to open inbound connections through your firewall with Application Proxy.
✅ Cost-effective. Demilitarised zones (DMZs), edge servers, and other sophisticated infrastructures are common requirements for on-premises solutions. Application Proxy is cloud-based, making it simple to use. You don’t need to update your network architecture or install any new appliances in your on-premises environment to use Application Proxy.
Data Subject Requests (DSR)
The General Data Protection Regulation (GDPR) of the European Union aims to preserve and enable individuals’ privacy rights within the EU (EU). Individuals in the EU (known as data subjects) have the right to access, retrieve, correct, erase, and restrict personal data processing under the GDPR.
Personal data is defined as any information relating to an identified or identifiable natural person under the GDPR.
A Data Subject Request, or DSR, is a formal request by a person to their organisation to take action on their personal data.
You can use the DSR case tool to:
✅ Build a new case for each DSR inquiry.
✅ Add people as members of the DSR case to control who has access to it; only members have access to it and can only view their cases in the list of cases on the DSR cases page in the compliance centre. Additionally, various permissions can be assigned to different members of the same case.
✅ To find all information made or uploaded by a certain data subject, use the built-in search.
✅ To narrow the search results, update the built-in search term and restart the search.
✅ Other content searches related to the DSR case can be added. This includes searches that yield partially indexed objects and Office Roaming Service system-generated logs.
✅ Export data in response to a DSR access or export request.
✅ Delete all cases when the DSR inquiry is finished. All searches and export jobs related to the case are removed as a result of this action.
Exchange Online Archiving
Microsoft Exchange Online Archiving is a Microsoft 365 cloud-based, enterprise-class archiving solution. Organisations can use Exchange Online Archiving to help with archiving, compliance, regulatory, and eDiscovery issues.
Exchange Online Archiving is a Microsoft online service that is designed to help fulfil the demands of robust security, reliability, and user productivity.
Litigation Hold
Put a mailbox on Litigation Hold to keep all of its contents, including deleted things and modified items’ original versions, safe.
When you put a mailbox on Litigation Hold, it also puts the user’s archive mailbox on hold (if it’s enabled). Deleted and changed items are saved for a set amount of time or until the mailbox is removed from Litigation Hold.
Retention Policies
Retention policies and retention labels with label policies are used to assign your content retention settings. You can use one or all of these techniques.
At the site or mailbox level, use a retention policy to assign the same retention settings for content, and at the item level, use a retention label to assign the same retention settings (folder, document, email).
If all documents in a SharePoint site should be kept for five years, for example, a retention policy is more efficient than applying the same retention label to all documents in that site. A retention policy, on the other hand, would not be able to distinguish between documents that should be kept for 5 years and those that should be kept for 10 years. You can use retention labels when you need to specify retention settings at the item level.
Insights by MyAnalytics
Microsoft Viva Insights gives you personal insights into two of the most important aspects of personal productivity: how people spend their time and with whom they spend it.
These advantages are available to you and your team after an administrator has set up Viva Insights in your company.
Office 365 Cloud App Security
Office 365 Cloud App Security is a subset of Microsoft Defender for Cloud Apps that provides enhanced visibility and control for Office 365. Threat detection based on user activity logs, discovery of Shadow IT for apps with similar functionality to Office 365 offerings, control app permissions to Office 365, and access and session controls are all part of Office 365 Cloud App Security.
The full feature list is available here.
Office 365 Data Loss Prevention
Microsoft launched the Security and Compliance Center for Office 365 in early 2017, allowing users to manage a variety of features, including data loss prevention.
The data loss prevention feature in Office 365 works similarly to other DLP tools in that it adheres to a set of rules. Data will be governed by policies defined in Office 365, which will send notifications when someone breaks a rule.
The DLP feature in Office 365 will automatically classify data and use the set policies to block unauthorised access to classified content and stop emails from being sent.
Office Message Encryption
Financial data, legal contracts, confidential product information, sales reports and projections, patient health information, and customer and employee information are all commonly exchanged via email. As a result, mailboxes can become repositories for large amounts of potentially sensitive data, and data leakage can pose a serious threat to your company.

Your organisation can send and receive encrypted email messages between people inside and outside your organisation using Office 365 Message Encryption. Outlook.com, Yahoo!, Gmail, and other email services are compatible with Office 365 Message Encryption. Email message encryption ensures that only the intended recipients can see the contents of the message.
Yammer
Yammer is frequently compared to Facebook for business. It has social networking features and can be accessed through a browser or as a standalone mobile app.
Yammer is only available to business users who are part of a Microsoft 365 Enterprise plan because it is a closed platform to which only employees within a corporate domain have access.
Ready to migrate for more security?
The digital world is rife with challenges, especially if your business doesn’t keep up with trends in the industry. Loss of data can happen at any time, which can give your competitors the upper hand and tarnish your reputation.
That’s why switching to Microsoft 365 Business Premium can be one of the wisest investments you can make.
If you feel your current solution is not delivering the necessary results, give us a call or book a 15-minute video call at a time that suits you. There’s no obligation to buy anything, ever. During this quick chat, however, we can come up with the perfect solution to your business’s technology requirements. Here’s our live calendar:
Here's our live calendar!Questions: [email protected]
Continue reading:
Security
13 Strategies To Make Your Cybersecurity Failproof
IT Infrastructure












Recent Comments