What and Where is the Cloud?
First things first: when we want to talk about ‘the cloud’, we need a bit of vocabulary – a bit like the Spanish or French classes back in school. Let’s start with server. Very simplified, a server is a powerful computer that provides one specific job to other computers. Data centres are centres that host a lot of data on said servers.
With those two things in mind, let’s jump into the cloud story, its benefits and disadvantages. By the end, we’ll wrap it up together and explain how Cyber Essentials plays into all of this.
What is the Cloud?
The cloud is used as a term for a series of on-demand, remote access, subscription services that exist on the internet. One commonly used cloud service is data storage. Instead of storing information directly on your own personal computer or phone, cloud-based data is stored elsewhere, not on clouds, but on servers housed in massive data centres. Examples are Google Drive, Dropbox, OneDrive, Apple iCloud, and IDrive.
Where is the Cloud?
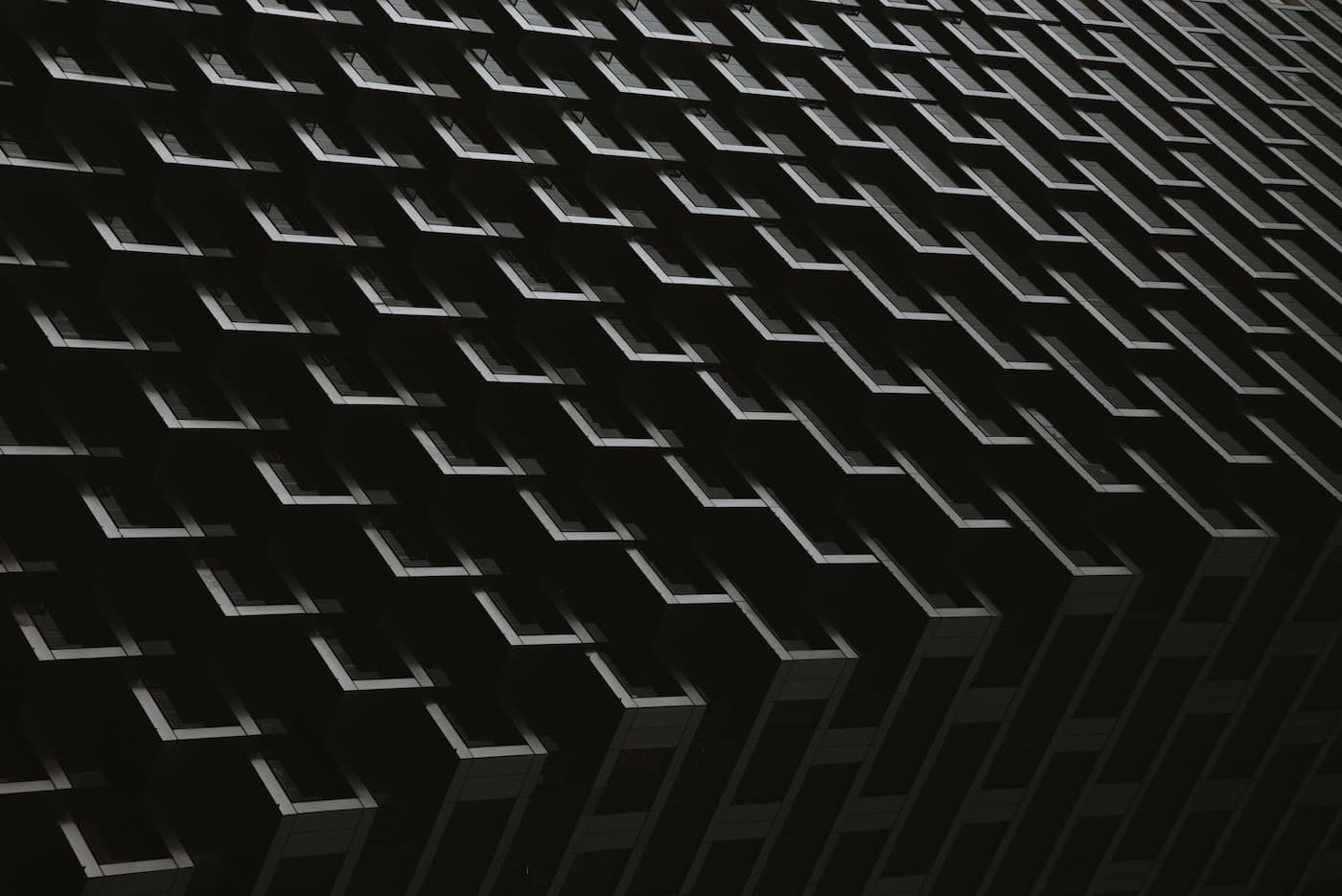
The cloud is a metaphor for the internet and for services that can seem quite abstract. The image of a cloud suggests ethereal, natural, and benign, it is everywhere but nowhere and belongs to no one or everyone. This metaphor is misleading, as, in reality, the cloud exists as row upon row of powerful computers with cables that radiate all over the world.
It is owned by a few of the world’s largest private organisations such as Amazon, Microsoft, Google or Apple and keeps millions of people’s data that is made accessible to them via the internet. The biggest data storage servers in the world are located in China, USA and India, some are even situated at the bottom of the ocean.
Cloud Computing ‘as a Service’ Model
A widely used service available in cloud computing is office software and web-based applications, which is known as Software as a Service or SaaS. An example of SaaS is Gmail and Yahoo email and Office 365 and Google Docs.
If we take Office 365 as an example, you can sign in to your Microsoft account on any machine and access Microsoft word where you will find your files. Neither the application Microsoft Word, nor those files are stored on your computer, but in the cloud, and this makes them accessible remotely from any computer as long as there is an internet connection.
Cloud computing allows users the flexibility to collaborate with others from any location.
Examples of other services that run their operations from the cloud include Youtube, Facebook, Zoom, Netflix and Spotify. Most will be located with the biggest cloud service providers, Amazon Web Services, Google Cloud Platform and Microsoft Azure.
In addition to SaaS, businesses that need to create websites and applications can rent cloud-based hardware and operating systems needed to run applications, this is known as Platform as a Service or PaaS. With PaaS, consumers do not have the responsibility of managing, updating and maintaining the platform that hosts the application and can therefore focus more on software development or providing other services to customers.
Infrastructure as a Service or IaaS is the most comprehensive cloud platform and is mainly used by full-time developers or large businesses. The cloud provider hosts the infrastructure components that were traditionally present in an on-premises data centre, including powerful servers, almost limitless storage, and networking.
Benefits of Cloud Services
When a business has a subscription for any of these services with a Cloud Service Provider (CPS), once they have made the initial cost to deploy their business across to the cloud, it saves them costly outlay for technology that may become out of date in a few years.
Another benefit of the ‘as a Service’ model, is that because a professional company is managing your technology, their level of support and maintenance, means more of your budget and time can be spent on business strategy and less on IT and security.
Security Risks of the Cloud
The chances are, your data is more secure in the cloud than on your own device within your own premises. The logic behind this comment is that most big cloud service providers spend millions of pounds managing and maintaining the security of their services. There are some customer responsibilities, however, and it’s worth noting that failure to meet consumer responsibilities is a leading cause of security incidents in cloud-based systems.
Minimise Risk with Basic Procedures
Use Multifactor Authentication
If you can access your data remotely, so can cybercriminals. Multifactor Authentication (MFA) gives a crucial layer of added security when logging into your cloud accounts.
Instead of just a password, MFA asks a user to provide another form of authentication, this might be a password plus a code received as an SMS or a fingerprint scan.
Limit and Monitor the Access of Your Users
Limiting access can limit the impact when accounting information like user names and passwords are stolen or a disgruntled employee wants to cause harm. Read more about this topic in our previous post here: User and Admin Accounts – Control the Access to Your Computer
Provide Anti-Phishing and Security Training
It is important that the individuals who use the system are educated about best practice behaviour and the tactics used by people who send ‘phishing’ emails.
‘Phishing’ is a term that describes the use of deception to manipulate people into revealing their security information. Phishing attacks are a common way that hacker’s access even the most secure cloud database.
Organise Data Back-Up
Most Cloud Service Providers give significant guarantees against the loss of data; however, no system is perfect. Major cloud providers have accidentally lost customer data. Ensure that your chosen CSP has data backup and recovery processes that meet your organisation’s needs.
Neutralise Threats for Peace of Mind
As more of our information and activities go online, cyber security has become a necessary part of life that keeps us safe from crime. Just like learning anything new, it can be broken down into small steps and implemented in bite-sized chunks.
Businesses of all sizes are at particular risk of cybercrime and would benefit from working towards Cyber Essentials which is a Government approved scheme. By implementing just five core controls that protect against most cyberattacks, businesses can ensure they are on the right track as well as demonstrate to their customers and suppliers that they are serious about cyber security.
Click here to find out more about Cyber Essentials.
As a Cyber Essentials Assessor, we are always happy to support your ambitions to become certified and want you to benefit from additional security and much more such as
✅ Becoming eligible to apply for Government tenders
✅ Reducing insurance premiums
✅ Avoiding GDPR fines
✅ Establish trust with suppliers and customers
And it’s not only about your business but the wider community. Every successful hack funds the cybercriminals and allows them to purchase more hardware and other tools to carry on their despicable profession.
So, if you want to take your business to the next level, give us a call or book a 15-minute video call at a time that suits you. There’s no obligation to buy anything, ever. During this quick chat, however, we can discuss what a Cyber Essentials certification would bring to your business and the process behind it.
Here's our live calendar!
Questions: [email protected]
Continue reading:
Creating an IT Compliance Policy – The 7 Things You Need to Consider
Ninja at the Gateway – The Secrets of your Router
Why You Need to Know About Cybercrime












Recent Comments